GSoC2018:Trust-based routing protocols framework
Main Page - Roadmap - Summer Projects - Project Ideas - Developer FAQ - Tools - Related Projects
HOWTOs - Installation - Troubleshooting - User FAQ - Samples - Models - Education - Contributed Code - Papers
Return to GSoC 2018 Accepted Projects page.
Project Overview
- Project name: Trust-based routing protocols framework
- Student: Jude Niroshan
- Mentor: Tommaso Pecorella
- Abstract: ns-3 contains different routing modules, both for IPv4 and for IPv6. None of them are trust-based routing protocols. Given the increasing interest on trust-based routing schemes to increase and improve the network resilience vs routing attacks, it would be useful to have a general approach for trust-based schemes. As a matter of fact, there are multiple trust-based extensions for well known protocol (e.g., AODV), but each one modifies in a particular way the single routing protocol, making it difficult to export the solution to other routing schemes. Therefore, it would be beneficial for many developers to have a generic trust-based framework which accommodates the alteration of well-known protocols to work as trust based protocols.
- Code: Github repository
- About me: I am an undergraduate student at the Sri Lanka Institute of Information Technology(SLIIT), Sri Lanka. I'm so excited to work with ns-3 community during the summer of 2018. You can find more about me on LinkedIn
Introduction
Networks are susceptible to attacks by malicious nodes that could easily bring down the whole network. Therefore, it is important to have a reliable mechanism for detecting and isolating malicious nodes before they can do any harm to the network. Usually, routing protocols discover usable multi-hop routes between source and destination nodes. However, some of the routes found and used may not be as reliable or trust-worthy as expected. Thus, finding a trusted route is an important component for enhancing the security of communication. Enhanced trust and security are achieved by the maintenance of a trust value by the nodes in the network. This factor is established and refined over time and it increases for each node when it participates successfully in data transmissions.
What is Trust value
Trust is a relationship established between two entities for a specific action. In particular, one entity trusts the other entity to perform an action. In this work, the first entity is called the subject, the second entity is called the agent.' [1]
Trust is a function of uncertainty. In particular, if the subject believes that the agent will perform the action for sure, the subject fully “trusts” the agent to perform the action and there is no uncertainty; if the subject believes that the agent will not perform the action for sure, the subject “trusts” the agent not to perform the action, and there is no uncertainty either; if the subject does not have any idea of whether the agent will perform the action or not, the subject does not have trust in the agent. In this case, the subject has the highest uncertainty.[1]
Trust value should represent uncertainty.[1] Uncertainly always stick to the probability which always has the value ranging from 0 - 1. Therefore, trust value will also be ranging from 0 - 1 by denoting the trust between nodes in the network.
- [1] Sun, Y.L., Yu, W., Han, Z. and Liu, K.R., 2006. Information theoretic framework of trust modeling and evaluation for ad hoc networks. IEEE Journal on Selected Areas in Communications, 24(2), pp.305-317.
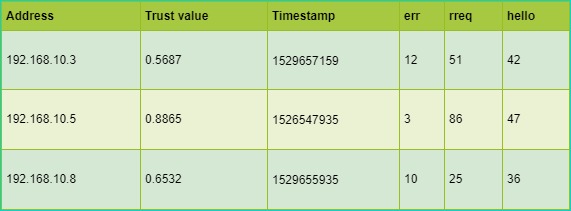
Trust value will be calculated based on different routing parameters(rreq, rply, err, etc) or routing metrics(bandwidth, cost, etc). Therefore, trust will become a routing metric which can be used to determine the optimal route for forwarding packets. Eventually trust value can be considered as a security factor for making the routing decision.
Administer trust values
There is a separate new table to hold the trust values in each node within the network. Trust values in ad-hoc networks will have no affect on the routing table.
Why need a trust based framework
Trust is a subjective measurement. There are many research papers have published which has various methodologies of calculating the trust value for the same routing protocol.
For e.g.: If we consider AODV routing protocol; following papers have came up with different approaches for trust value calculation.
- [2] Li, X., Lyu, M.R. and Liu, J., 2004, March. A trust model based routing protocol for secure ad hoc networks. In Aerospace Conference, 2004. Proceedings. 2004 IEEE (Vol. 2, pp. 1286-1295). IEEE.
- [3] Marchang, N. and Datta, R., 2012. Light-weight trust-based routing protocol for mobile ad hoc networks. IET information security, 6(2), pp.77-83.
- [4] Pushpa, A.M., 2009, December. Trust based secure routing in AODV routing protocol. In Internet Multimedia Services Architecture and Applications (IMSAA), 2009 IEEE International Conference on (pp. 1-6). IEEE.
Current NS-3 version(ns-3.28) does not welcome trust based routing protocols by default. If someone wants to simulate a trust based protocol in NS-3, there are lot of changes needs to be done in many concrete level classes. This is cumbersome and it's against the conventions that we follow from the maintenance point of view. NS-3 cannot define only one way of calculating trust value as each of the above mentioned methods/approaches have written to serve specific concerns/issues. Therefore, it's clear that allowing any custom trust calculation run through a framework is a better move from NS-3. This will help the developers to try out trust based frameworks in NS-3 with minimal amount of coding.
Technical Approach
Trust Table
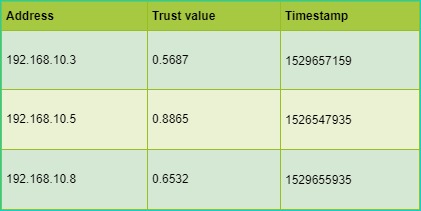
Similar to routing table, there will an additional table called trust table. It is required to have a trust table per each node within the network. Trust framework has a trust table which has columns of Address, Trust value, Timestamp. Each row in the trust table represent a trust record for directly connected (1 hop) nodes for a considering node. One row in trust-table.h is represented by trust-entry.h object.
Users can extend trust-entry object and add additional columns as they wish. This will give great flexibility over adding more attributes for the trust table.
Trust calculation algorithm
Almost all the research papers published have different algorithms for trust calculation. Therefore, the framework has allowed any trust calculation algorithm to work by simply defining how the calculation should work.
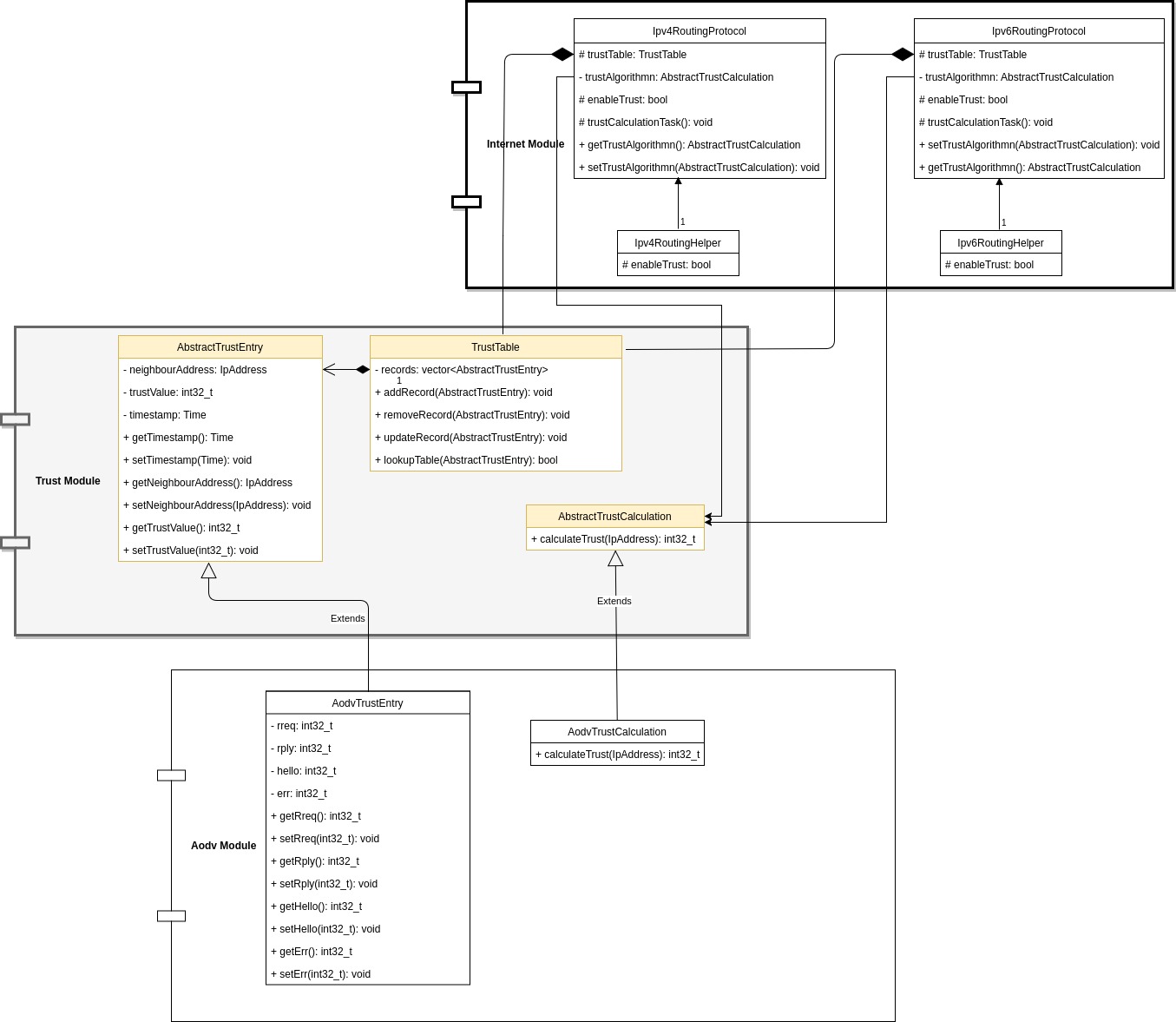
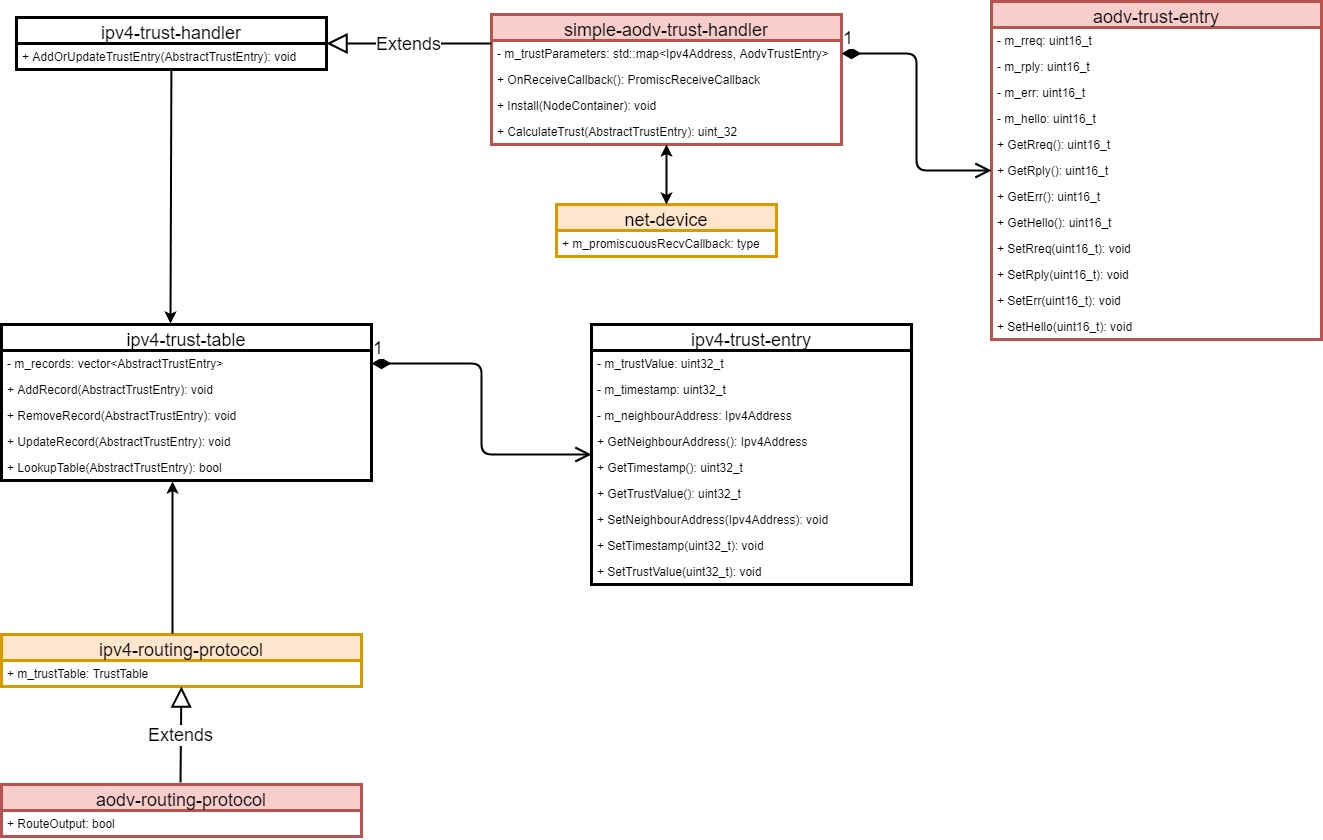
simple-aodv-trust-handler is proper example usage of trust calculation of the trust framework. trust-handler is the abstract class which has CalcuateTrust() method. This method must be implemented in a concrete class.
Architecture
There will be a new trust module consists of abstract classes which can be extended and implemented as the user's preferences. Users can extend the abstract-trust-calculation class and implement their own logic to calculate the trust value.
trust-table is a new table which is similar to routing table. Trust table contains trust value related information for directly connected nodes. Users will be able to add new properties to trust table as they wish. At the same time, trust calculation logic is also feasible to change according to the above framework structure. As you can see in UML, any user can define the trust calculation algorithm by simply extending the AbstractTrustCalculation class.
Project Timeline
Week 1 (May 14 - May 20)
- Clone appropriate git repository
- Investigate on the internal and external network attack types
Week 2 (May 21 - May 27)
- Create a well structured UML diagram
- Create a simple simulation with 2 network nodes. Analyze the data packets that transfer between those nodes.
- Create the Abstract trust table class
Week 3 (May 28 - June 3)
- Create a new ns-3 module called 'trust'
- Move abstract classes into that new module and test (Done, but raised dependency issues)
Week 4 (June 3 - June 10)
- Write up a trust implementation before making a abstract module
Note: It has decided to remove the trust module until we have a fully working trust framework. Therefore, all classes planned to go to new trust module has been moved to internet module.
- Test the AODV specific implementation
Week 5 (June 11 - June 17)
- Write doxygen documentation for abstract classes implemented inside internet module
abstract-trust-entry.h abstract-trust-calculation.h trust-table.h ipv4-routing-helper.h
- Modify the helper classes to place the main boolean flag to turn on or off the trust based framework
Ipv4RoutingHelper::Ipv4RoutingHelper (bool enableTrust)
{
this->enableTrust = enableTrust;
}
Week 6 (June 18 - June 24)
- Documentation and added more description about the trust framework
- Modified the aodv-routing-protocol.cc to collect metrics for the trust calculation
Week 7 (June 25 - July 02)
- Re-designed the architecture for the trust framework as we have concerns about changing the protocol classes
- New promiscuous callback function considered to collect the metrics for trust value calculation
Week 8 (July 03 - July 10)
- Created a simple simulation with a simple promiscuous callback to collect the metrics for trust calculation
- Removed the boolean flag which is unnecessary code. (We will decide whether to switch to trust tables if we have a trust table for a given node)
Week 9 (July 10 - July 17)
- Re-designed the trust framework architecture as follows: